Cbrom Exe Bios
• • • • Reading Time: ~ 6 min. By Marco Giuliani In the past few weeks a Chinese security company called blogged about a new BIOS rootkit hitting Chinese computers. This turned to be a very interesting discovery as it appears to be the first real malware targeting system BIOS since a well-known proof of concept called IceLord in 2007. The malware is called Mebromi and contains a bit of everything: a BIOS rootkit specifically targeting Award BIOS, a MBR rootkit, a kernel mode rootkit, a PE file infector and a Trojan downloader. At this time, Mebromi is not designed to infect 64-bit operating system and it is not able to infect the system if run with limited privileges.
Apr 20, 2002 - Ive just extracted my bios from a MSI 9105LR which has Fastrak100 Lite onboard raid, had a go at removing the Fastrak100 Lite code and then. Ensure that you have CBROM.EXE and TIFF2AWBM.EXE (from AWBMTools) somewhere in your PATH (if you don't know what this means, it's best that you don't play with your BIOS).The easiest way of ensuring this is to put all the EXEs in the same folder as your BIOS file 3. Blur oyunu crack dosyas indir.

The infection starts with a small encrypted dropper that contains five crypted resource files: hook.rom, flash.dll, cbrom.exe, my.sys, bios.sys. The goal of these files will be presented later in this analysis. The infection is clearly focused on Chinese users, because the dropper is carefully checking if the system it’s going to infect is protected by Chinese security software Rising Antivirus and Jiangmin KV Antivirus. To gain access to the BIOS, the infection first needs to get loaded in kernel mode so that it can handle with physical memory instead of virtual memory. Many of you may recall the old CIH/Chernobyl infection, the infamous virus discovered in 1998 that was able to flash the motherboard BIOS, erasing it.
Even CIH needed to gain kernel mode access to reach the BIOS, though at the time the virus was exploiting a privilege escalation bug in Windows 9x operating system which allowed it to overwrite the Interrupt Descriptor Table with its own payload from user mode, then triggering the overwritten interrupt handler and its malicious code is executed in kernel mode. Mebromi does not use such kind of privilege escalation trick anymore, it just needs to load its own kernel mode driver which will handle the BIOS infection.
To do so, it uses two methods: it could either extract and load the flash.dll library which will load the bios.sys driver, or it stops the beep.sys service key, overwriting the beep.sys driver with its own bios.sys code, restart the service key and restore the original beep.sys code. The bios.sys driver is the code which handle the BIOS infection. To read the BIOS code, it needs to map the physical memory located at physical memory address 0xF0000, this is where the BIOS ROM usually resides. Once read, the driver verifies if the BIOS ROM is Award BIOS, by checking the presence of the string: $@AWDFLA.
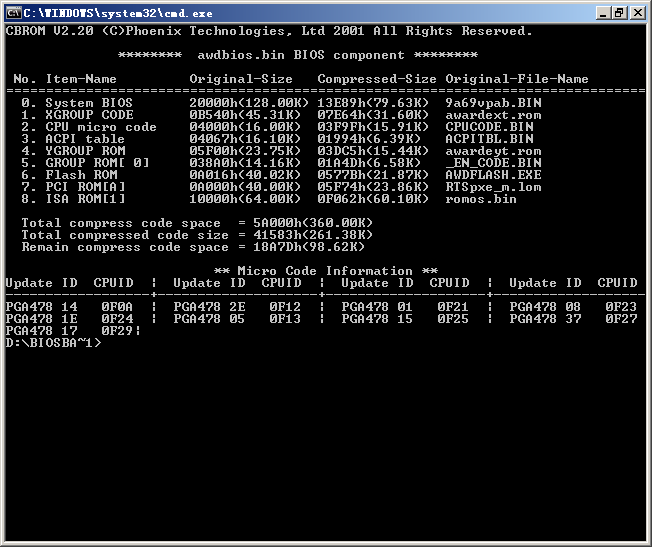
If found, the driver tries to locate the SMI port that will be used by the rootkit to flash the BIOS ROM. If the BIOS ROM matches the string, the rootkit saves a copy of the BIOS to the file C:bios.bin and pass the next step to the user mode component of the infection. The dropper extracts two files: cbrom.exe and hook.rom. Cbrom.exe is a legitimate tool developed by Phoenix Technologies, used to modify the Award/Phoenix BIOS ROM binaries. Hook.rom is the rootkit ISA BIOS ROM that is added to the BIOS binary, containing the rootkit infection.
Download siemens lady 45 bedienungsanleitung pdf free software. Take full advantage of related PDF area to locate several other relevant pdf for SIEMENS LADY 45 MANUAL DOWNLOAD, just in case you missed your desired topic.